I’ve found that the information that’s out there about email authentication is either too detailed or too high level. So I wanted to produce a quick guide for administrators that’s somewhere in between.
We have three principle technologies at play. These technologies work together to provide an email security foundation.
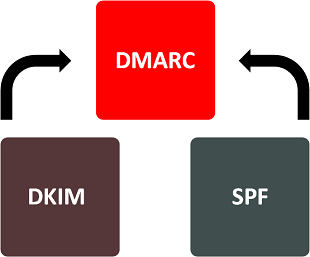
They are:
- Domain-based Message Authentication, Reporting & Conformance (DMARC)
- Sender Policy Framework (SPF)
- DomainKeys Identified Mail (DKIM)
These technologies protect the recipient of the email more than the sender. That is the validate the authenticity of the email that you are SENDING. However large scale adoption means that the online community is able to come together to authenticate each other’s email traffic to help eliminate the effectiveness of phishing and spam emails.
SPF
There are two ‘from’ addresses in an email. The ‘header from’ (AKA friendly from) and the ‘envelope from’ (AKA return path). An organisation hosts its own SPF record in DNS. This record can be used by the receiving organisation to confirm that mail received is from a valid source. That is the receiving organisation will check the DNS records for domain in the ‘envelope from’ field within the email header. Eg “contoso.com” to see if there is an SPF record. If there is, then the server will check to see whether the mail was received from a server matching this record. An example SPF record would be as follows:
|
1 |
[cc lang="text"]v=spf1 ip4:232.198.111.122 include:mail.contoso.com -all[/cc] |
If you’d like more information please look at this article.
DKIM
DKIM adds a digital signature the header section of an email. This uses public key cryptography to ensure that the email was from a genuine source and that the message hasn’t been tampered with or altered en-route.
The sending server creates a signature using it’s private key. This can be decrypted using the public key, which is stored in a text file within the sender’s DNS. Due to the high level of security provided by public key cryptography, this method gives those receiving the email peace of mind that the email is genuine.
An example DKIM record would be as follows:
|
1 |
[cc lang="text"]v=DKIM1; p=Es34dfgRGE55ehYRJ54JYRsfMTYesfsdNTNJSRefdgGg54t35tJSR[/cc] |
DMARC
This relatively recent authentication method was developed in 2007 by PayPal, with collaboration later being offered by Yahoo! and Google.
DMARC is like the ‘digital doorman’ ensuring that every email’s name is on both the SPF and DKIM list. DMARC will match the ‘header from’ domain name with the ‘envelope from’ domain name obtained from the SPF check, and will also match the ‘header from’ domain name with the ‘d= domain name’ in the DKIM signature. As well as carrying out these tests, DMARC is also used to inform recipient mail servers on what to do with any email that is suspected of not being genuine.
The sender can choose to:
- Monitor all mail to gain an understanding of misuse of their brand name through spam email and to ensure genuine mail is authenticating properly.
- Quarantine messages that fail DMARC ie ensure it lands in the recipient’s spam folder
- Reject messages that fail DMARC authentication ie request that the recipient’s email server doesn’t deliver the message at all.
An example DMARC record would be as follows:
|
1 |
[cc lang="text"]"v=DMARC1; p=reject; pct=100; rua=mailto:postmaster@contoso.com"[/cc] |
It is a combination of SPF, DKIM and DMARC together that offers confidence and security to businesses, customers and other internet users that an email is genuine and not a phishing attempt or spam.